V4bel
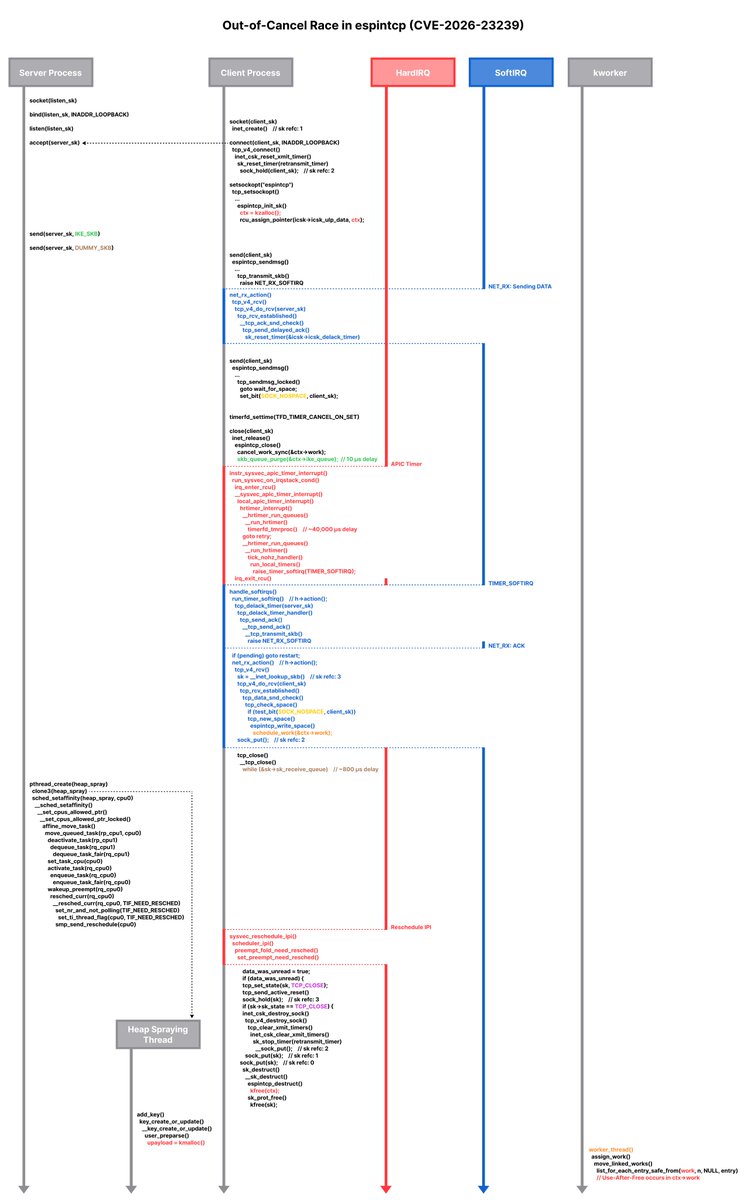
I discovered a race-based vulnerability class in the Linux kernel: "Out-of-Cancel" A structural flaw where cancel_work_sync() is used as a barrier for object lifetime management, causing UAF across multiple networking subsystems. I wrote an exploit for CVE-2026-23239 (espintcp). It interleaves Delayed ACK timers, NET_RX softirqs, timerfd hardirqs, workqueue scheduling, and CFS scheduler manipulation to hit a ~Xµs race window. Blog: https://v4bel.github.io/linux/2026/03/23/ooc.html This is the race scenario diagram 😁: